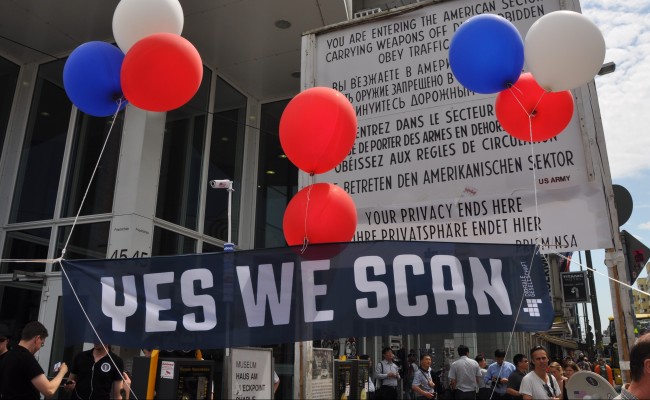
CISA Bill Passes Senate; Flaunts Privacy Concerns and Safe Harbor Hopes
The much-anticipated Cybersecurity Information Sharing Act (CISA) cleared the Senate hurdle Tuesday, and is now in conference. Rather impressively, every major privacy objection to the bill (many of which were actively being addressed by proposed amendments) was left unaddressed in the final version — including ones that would have taken at least some steps to address the US-EU Safe Harbor shortcomings and increase the likelihood of a “Safe Harbor 2.0“.
Here is a round-up of comments and coverage, with some additional remarks:
- The EFF (as to be expected) weighs in with disapproal:
The bill is fundamentally flawed due to its broad immunity clauses, vague definitions, and aggressive spying authorities. The bill now moves to a conference committee despite its inability to address problems that caused recent highly publicized computer data breaches, like unencrypted files, poor computer architecture, un-updated servers, and employees (or contractors) clicking malware links.
- Trevor Timm of the Freedom of the Press Foundation is scathing, calling the Senate “ignorant” on cybersecurity and the CISA a mere “surveillance bill”:
Under the vague guise of “cybersecurity”, the Senate voted on Tuesday to pass the Cybersecurity Information Sharing Act (CISA), a spying bill that essentially carves a giant hole in all our privacy laws and allows tech and telecom companies to hand over all sorts of private information to intelligence agencies without any court process whatsoever. Make no mistake: Congress has passed a surveillance bill in disguise, with no evidence it’ll help our security.
- In our view, Wired puts succinctly one of the key privacy flaws of the bill:
… privacy advocates and civil liberties groups see CISA as a free pass that allows companies to monitor users and share their information with the government without a warrant, while offering a backdoor that circumvents any laws that might protect users’ privacy. “The incentive and the framework it creates is for companies to quickly and massively collect user information and ship it to the government,” says Mark Jaycox, a legislative analyst for the civil liberties group the Electronic Frontier Foundation. “As soon as you do, you obtain broad immunity, even if you’ve violated privacy law.”
(In our view, while it might seem “fuzzy,” this point is dead-on. Companies are beasts of regulation; when regulation then gives them a free pass from potential huge liability, along with the government kudos that come with “pre-emptive voluntary cooperation”, they will quickly see the cost-benefit advantage and take the deal. This kind of incentive set is exactly opposite of one which would encourage companies to focus on cybersecurity and respect the privacy of their users.)
- NPR has a fairly even-handed attempt (in their trademark “scorecard” style) to make something out of the CISA, but comes up short, noting on one of the most fundamental points put forth in favor of the bill that “There are [already] existing initiatives, coordinated by Homeland Security and the National Institute of Standards and Technology, to share threat information. There are also subscription services in the private market.” That leaves company immunity for privacy violation as the “big” thing CISA adds — not new, helpful “pipelines” to share threat information.
- Finally, A recent InsideSources piece connects the CISA to Safe Harbor in an unhappy way:
Connecticut Democratic Sen. Chris Murphy withdrew an amendment that would have included the Judicial Redress Act in a vote on CISA over concerns it wouldn’t receive due consideration amid the broader fight. Many including Wisconsin Republican Rep. Jim Sensenbrenner, who authored the bill in the House, cite the legislation as a necessary step in getting the EU to agree to a new “Safe Harbor 2.0” agreement.
So let’s see: we have a bill that opens the doors once again to large-scale warrantless ingest of private information to government intelligence organizations just months after the government’s own direct mass warrantless surveillance programs had been “stopped”; grants a new form of immunity to companies for privacy violations (disrupting extensive progress in the other direction that has been made of late); fails to provide any judicial redress to EU citizens for privacy violations which is sorely needed to help re-establish Safe Harbor; and provides no new cybersecurity intelligence advantage. Color us unimpressed; indeed, rather distressed. We hope the bill is improved in conference, and if not, vetoed (though this is estimated to be unlikely).
Leave a comment